
When a 404 Turns Into a Jackpot

TL;DR
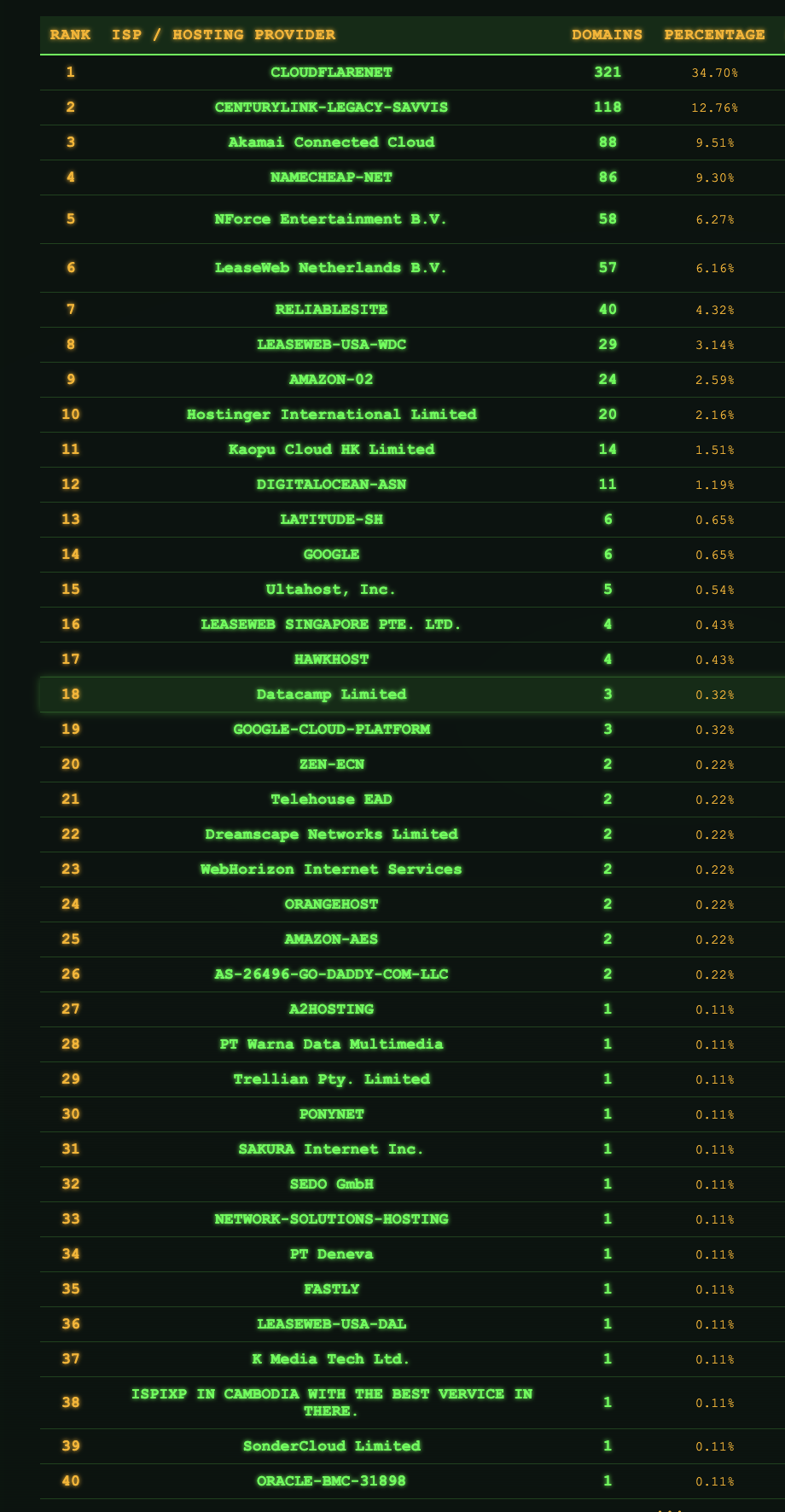
While securing a large entertainment company with more than 50,000 employees, a routine DNS scan revealed an abandoned Shopify subdomain that was hijacked within 24 hours, transforming from a "Shop Not Found" error into a live gambling storefront. What appeared to be a simple subdomain takeover turned out to be an industrial-scale gambling network spanning 500+ active brands across multiple cloud providers (Cloudflare, AWS, GCP, Akamai, Oracle).
The operation uses legitimate-looking e-commerce storefronts equipped with enterprise marketing stacks—complete with analytics, A/B testing, session replay, and GDPR banners—to camouflage gambling sites and exploit SEO rankings. The attack vector exploits abandoned SaaS mappings where DNS records remain after service decommissioning. The lesson: monitor subdomain drift continuously and reclaim abandoned mappings before attackers turn your 404 into their jackpot. We've developed a tool to quickly check if your company is affected by this vulnerability.
The Misconfiguration That Wasn't
It started the way most dull recon stories begin - with a DNS drift.
Our scanner flagged a tiny change on a customer's subdomain mapped to a SaaS storefront one of those shops.myshopify.com style endpoints.
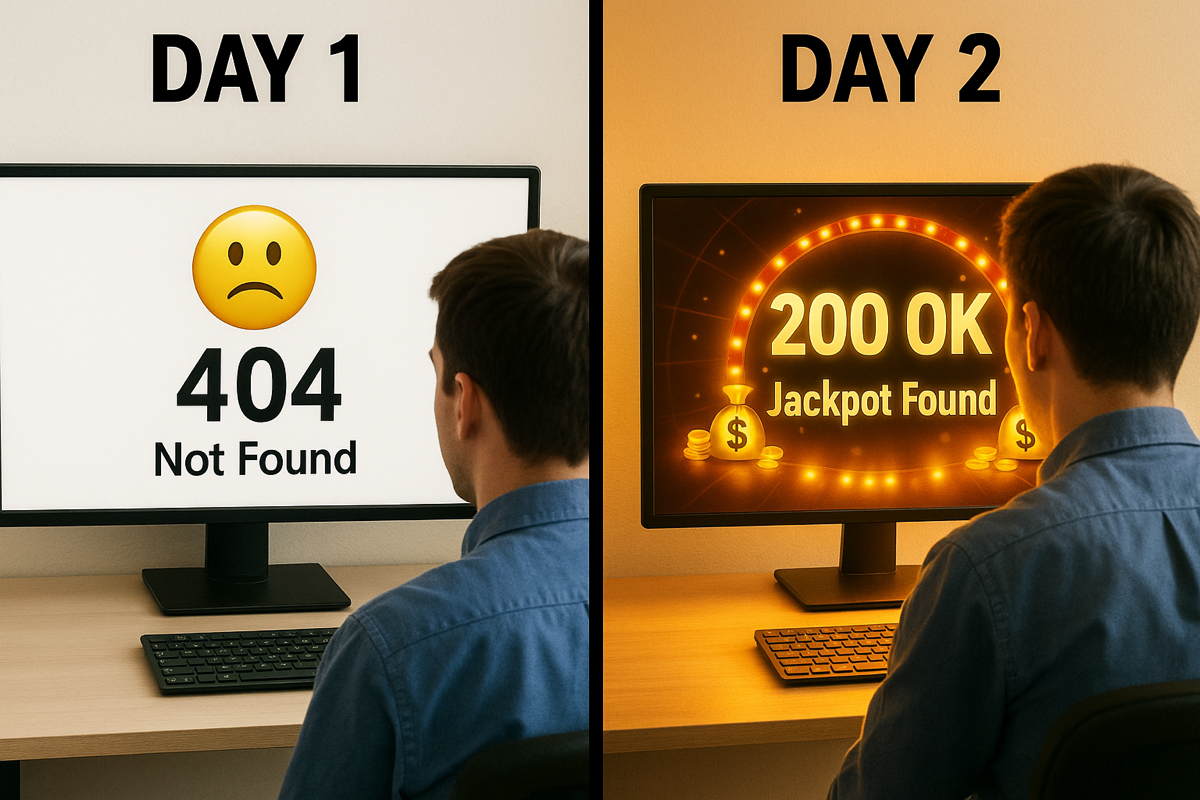
Day 1: ERROR 1001 / 409 - "Shop Not Found."
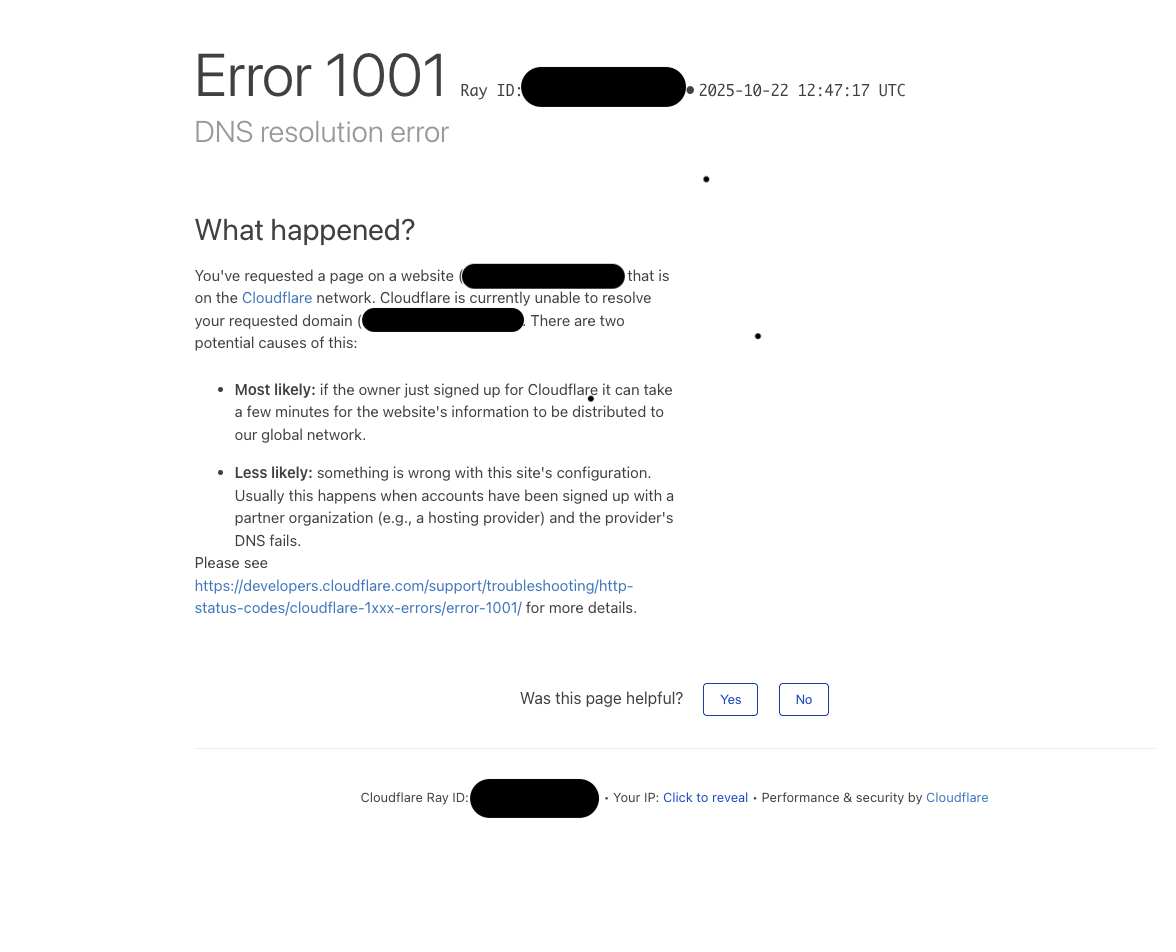
Day 2: HTTP 200 OK and suddenly, a live store under the customer's name.
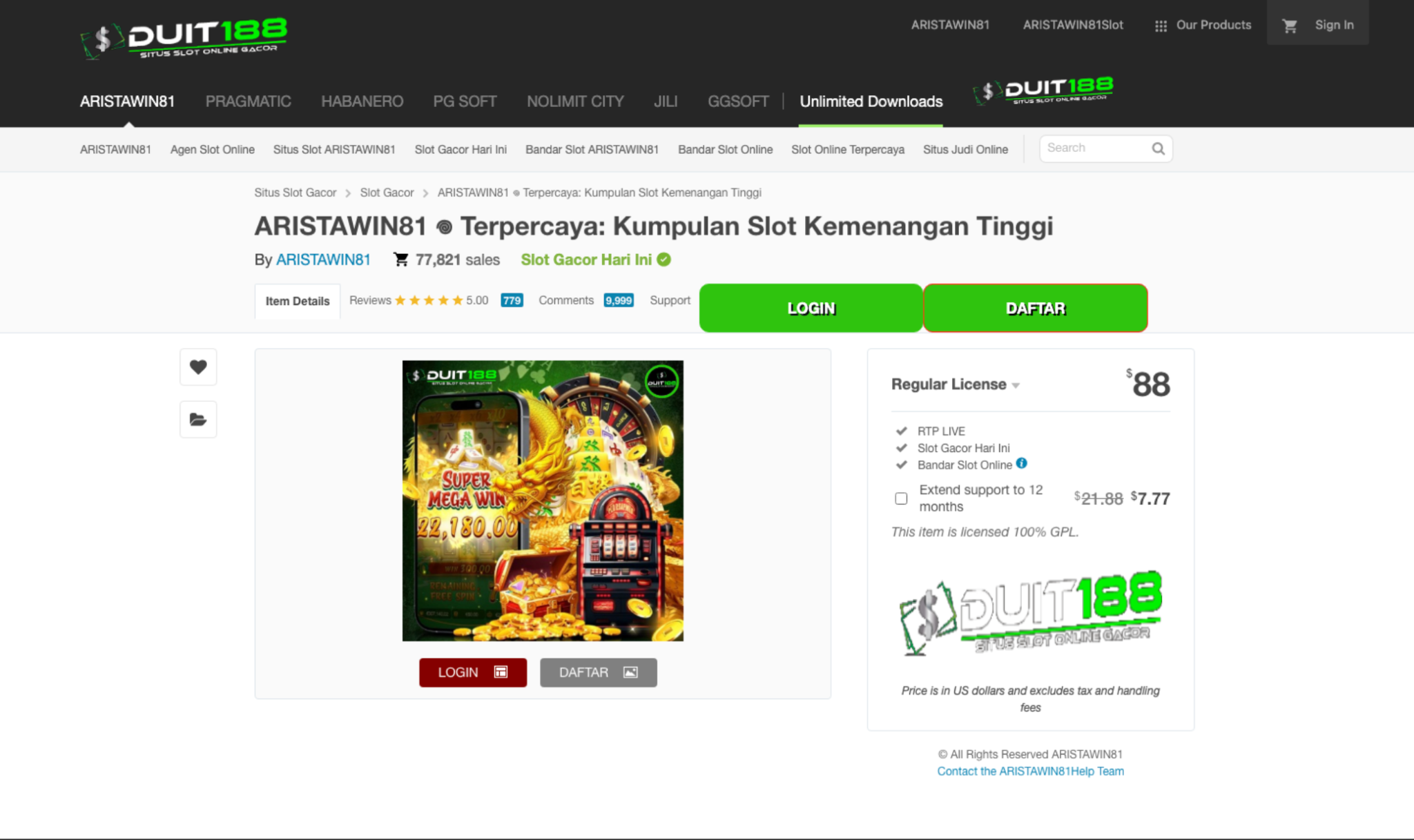
An abandoned Shopify mapping (shop.organization.com → shops.myshopify.com) remained in DNS after the original store was removed. Since Shopify will accept a custom domain that already resolves to its infrastructure, an attacker can simply register a new Shopify store and claim any potential abuseable hostname - instantly serving their own controlled content under the victim's subdomain (HTTP 200) and inheriting the domain's SEO and trust signals.
In the example above, we can see a specific casino being promoted in Malay - we did not observe any potential indication that the casino in question was part of this campaign, but we suspect that some sort of affiliation is involved by a third party of the casino.
On paper, it was just another "misconfigured CNAME → takeover risk", potentially closing the incident and moving on. Instead, we looked deeper and what we found went way beyond a simple DNS mistake.
Pulling the Thread
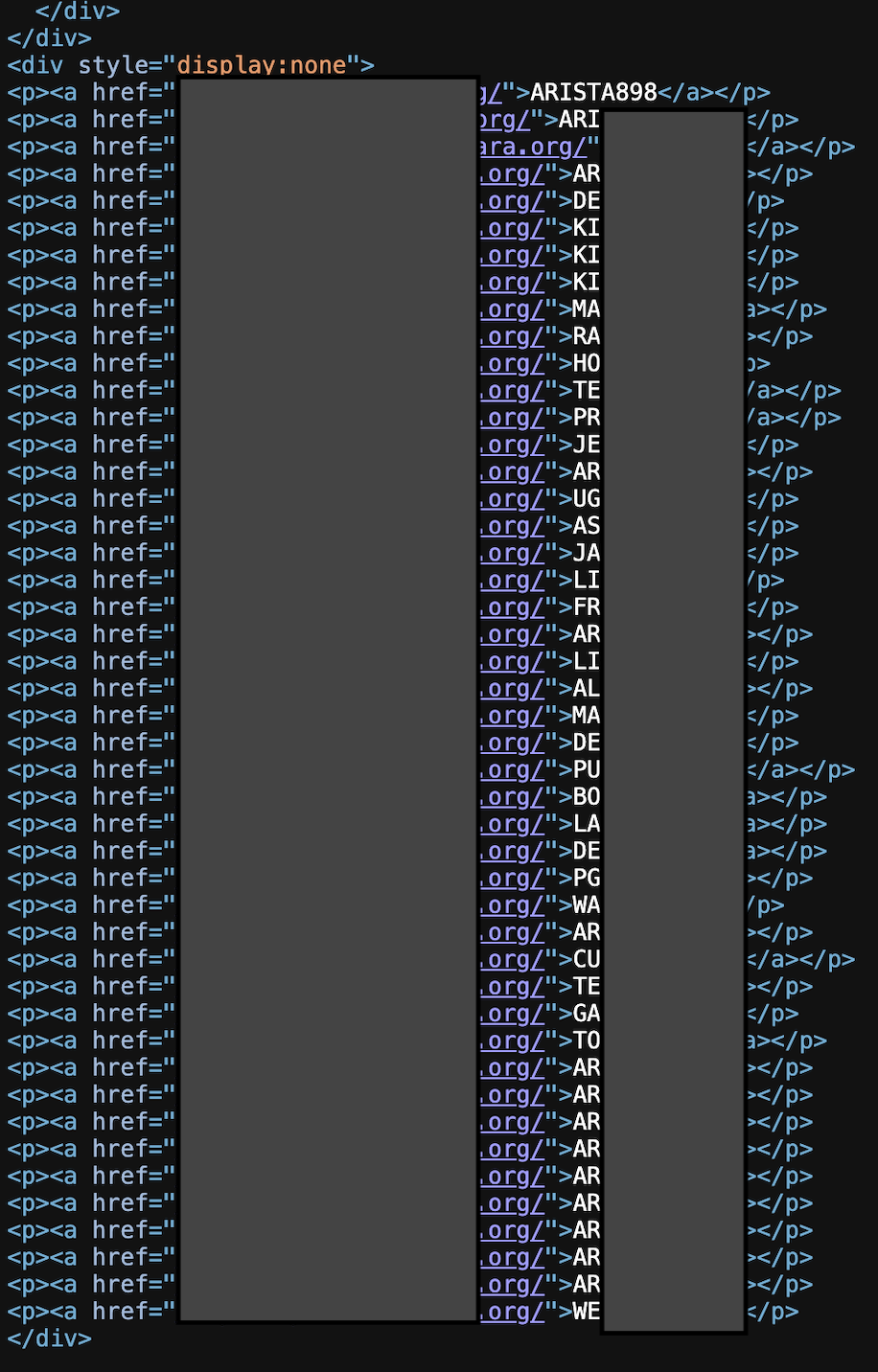
Once the takeover was confirmed, we looked under the visible storefront, the quiet lower half of the DOM.
This wasn't a random defacement or phishing kit.
It was a polished e-commerce landing page that looked perfectly legitimate yet funneled visitors into gambling sites.
And it wasn't running on throwaway code.
It carried:
- real marketing pixels
- real session-replay tooling
- real consent/GDPR banners
- real performance beacons
- real A/B-testing loaders
Someone had rebuilt a full enterprise-grade marketing stack, the same stack real businesses pay thousands a month to use but pointed it at online casinos.

The Network Unfolds
The deeper we went, the clearer the pattern became.
This wasn't one lucky hijack, it was a coordinated network of storefront-style pages, each posing as a normal product or marketplace listing.
Many shared a hidden DOM structure near the bottom packed with outbound links to gambling brands and campaign IDs belonging to the same operator.
That structure was the key: a repeating, templated element quietly connecting otherwise unrelated domains.
Enumerate the brands, and you find mirrors.
Follow the mirrors, and you map the infrastructure.
Each page referenced dozens of gambling brands, sometimes 20, 50.
That's industrial-scale brand proliferation: take down one, and the rest stay live.
Using those hidden brand strings as search seeds, we mass-scanned for variants across common TLDs, certificate-transparency logs, and shared IPs.
The results were staggering over 500 active brands, each with multiple domains spread across Cloudflare, Akamai, AWS, GCP, ORACLE, and others.

Behind them stood a long list of legitimate companies whose infrastructure or assets had been misused to lend credibility without their knowledge.

Why Clone the Marketing Stack?
Because stealing HTML doesn't scale.
The operators weren't cloning full sites; they were publishing gambling storefronts under valid, trusted domains that looked like product pages to crawlers.
To maintain authenticity, brand groups shared overlapping marketing fingerprints:
- similar analytics or tag IDs
- matching consent frameworks in certain templates
- common performance-monitoring and A/B-testing payloads
- the same overall "this is a real business" signals
This camouflage works on multiple fronts:
- Legitimacy camo defenders expect those scripts on those pages.
- SEO advantage "product" pages rank far better than "casino" pages.
- Attribution laundering traffic appears as normal browsing, not betting.
- Cost shifting + data pollution victims absorb analytics and RUM costs.
Beyond brand abuse, it creates real operational impact: inflated analytics bills, contaminated data, and the silent use of legitimate infrastructure to push illicit content.
Anatomy of the Operation
This campaign wasn't freelance improvisation; it was organized infrastructure.
- Centralized template control - multiple layouts, but updates (footers or scripts) propagate across dozens of domains through shared storage links and marketing keys.
- Tiered infrastructure - link hubs, primaries, mirrors, and clean decoys.
- Redundant entry points - several "safe" URLs route to the same brand.
- Active management - hidden link lists evolve as brands appear or retire.
- Paid traffic acquisition - ad pixels and conversion tags confirm investment.
- Shared telemetry - session replay and error tracking operational network-wide.
- SEO engineering - product schema and shopping context to boost ranking.
This isn't "I made a phishing page."
This is "I run a distributed content-delivery network and gambling is the payload."

The SaaS Doorway
The entry vector was painfully simple: an abandoned SaaS mapping.
- A company uses a third-party storefront service.
- They decommission it but leave DNS intact.
- The vendor still honors custom-domain claims.
- The attacker claims it and serves their own content under that brand.
Continuous recon catches that instantly.
Without it, discovery happens when Google indexes the new content or when marketing receives an email titled:
"Why are we advertising gambling?"

The Bigger Lesson
A 404 or 409 on a SaaS-mapped subdomain isn't harmless noise, it's an early-warning indicator.
If you don't reclaim it, someone else will and they can attach it to a network like this in minutes.
Monitor for drift.
Reclaim what's yours.
Don't let a 404 turn into someone else's jackpot.
Take action
This campaign is active. We can quickly test whether your domains are exposed, including unclaimed SaaS bindings and dangling subdomains.
Get a free exposure check: Contact us and we'll run the scan, share a short report, and help you neutralize any takeovers fast.
.svg)
